Source Link Privacy.

Tarlogic Security has detected a backdoor in the ESP32, a microcontroller that enables WiFi and Bluetooth connection and is present in millions of mass-market IoT devices. Exploitation of this backdoor would allow hostile actors to conduct impersonation attacks and permanently infect sensitive devices such as mobile phones, computers, smart locks or medical equipment by bypassing code audit controls.
Update: The ESP32 “backdoor” that wasn’t.


Well… Shit.
There are so, so, so, many ESP32’s in not just my house, but practically everyone I know.
There outta be fines for this BS.
You’re fine. This isn’t something that can be exploited over wifi. You literally need physical access to the device to exploit it as it’s commands over USB that allow flashing the chip.
This is a security firm making everything sound scary because they want you to buy their testing device.
You don’t need physical access. Read the article. The researcher used physical USB to discover that the Bluetooth firmware has backdoors. It doesn’t require physical access to exploit.
It’s Bluetooth that’s vulnerable.
https://www.bleepingcomputer.com/news/security/undocumented-backdoor-found-in-bluetooth-chip-used-by-a-billion-devices/
I just re-read the article and yes, you still need physical access.
The exploit is one that bypasses OS protections to writing to the firmware. In otherwords, you need to get the device to run a malicious piece of code or exploit a vulnerability in already running code that also interacts with the bluetooth stack.
The exploit, explicitly, is not one that can be carried out with a drive-by Bluetooth connection. You also need faulty software running on the device.
“Depending on how Bluetooth stacks handle HCI commands on the device, remote exploitation of the backdoor might be possible via malicious firmware or rogue Bluetooth connections.”
I of course don’t know details but I’m basing my post on that sentence. “Backdoor may be possible via … rogue Bluetooth connections.”
I really wish these articles just tell us what these scenarios are. I understand companies need publicity or need to sell software but if it isn’t replicatable and the article says “might be possible” it kind of sounds like a secuity sales pitch.
This part basically sounds more like a software issue where the attacker has a way in already. The system is already vulernable at this point before using the exploit found.
I don’t think there’s enough information out yet.
It is very interesting though.
I do have a few outside. Probably not the best security-wise. Haha. Those are the first to get patched when one comes out.
Security wise, unless you are being specifically targeted by someone, you are almost certainly fine. And if you are being specifically targeted, I think someone hacking your ESPs is the least of your worries. A malicious attacker that knows your physical location can do a lot more scary things than just spying through ESPs.
Just wait until a jester creates a software that sends an erase flash backdoor command to any BT device it sees.
One of my friends is a type I diabetic. He had some sort of smart thingamajig in his teenage years for measuring blood sugar, so you could monitor it over time or warn your family if you’re in some critical situation.
The jester may mean simply to prank, but they may well have blood on their hands if they fuck up medical devices such as that one.
And runs with an USB cable flashing other peoples ESPs to ruin everyone’s day
In that case, how long til some open source project uses it to make a custom firmware to bypass the manufacturer bs and integrate my cheap IoTs seamlessly into Home assistant?
You can already reflash a lot of devices for this purpose. And you could use esp-home to customise once reflashed
Really? Where can I find this
Heres the top google link i found: https://randomnerdtutorials.com/how-to-flash-a-custom-firmware-to-sonoff/
Esp-home is available as a HA addin, docs here: https://esphome.io/
Thanks
Esp-home also works with the older esp-01 - it was released as a wifi module so there are only two gpio’s, but thats enough for a lot of home automation stuff.
Here’s one i have connected to HA, where HA uses rest-api to capture some data from a game called tacticus, and it shows my available tokens for guild raid and arena
Tasmota is another option if they have your specific device in their list. Otherwise you have to do some debugging to figure out what gpio or i2c address to use.
https://esphome.io/
I think we are basically already there with ESPs :D.
Wrong. Read the analysis. It is a BT vulnerability. One can probably design a cheap attack system that just sends a erase flash command to any BT device in reach, instantly bricking every BT enabled ESP32 device.
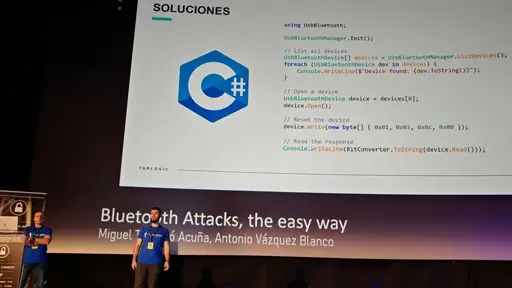
Just reread it and no, it’s not a BT vulnerability. The “erase flash” command is something that has to be done by software running outside the BT stack. You can even see that inside the slides. The
UsbBluetoothsoftware is connected to the device with the flawed bluetooth chipset.The vulnerability is that if you have this chipset and compromised software, someone can flash the chipset with compromised flash. They even say that it’s not an easy attack to pull off in the article.
In otherwords, the attack is something that can only be pulled off if there’s also a security vulnerability within other parts of the hardware stack.
Yeah, that’s not the main concern.